RSA Explanation Foggy Breach Details
RSA explanation foggy about breach details highlights a critical issue in cybersecurity. The lack of clarity surrounding the specifics of a recent breach raises serious questions about transparency and communication in these situations. How much information should be released, and when? This blog post delves into the complexities of this issue, exploring the various facets of the breach and the potential consequences.
We’ll examine the RSA encryption algorithm and different types of security breaches, exploring the potential consequences of such incidents. Understanding the “foggy” aspect of this breach requires examining the reasons behind the ambiguity, and what this might say about security practices more generally. Further, we’ll consider communication strategies and legal/ethical implications of incomplete disclosure, potential impacts on finances, reputation, and user trust, and methods for addressing the lack of clarity.
Overview of RSA and Security Breaches
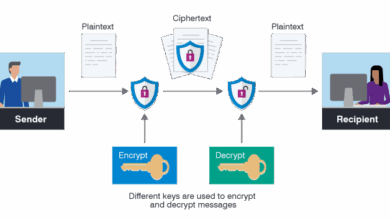
The RSA algorithm, a cornerstone of modern cryptography, underpins many secure online interactions. Understanding its workings and potential vulnerabilities is crucial for anyone dealing with sensitive data. This exploration delves into the RSA encryption method, the various ways it can be compromised, and the broader implications of such breaches. We’ll also compare RSA to other common encryption techniques to highlight its strengths and weaknesses.RSA, or Rivest-Shamir-Adleman, is an asymmetric encryption algorithm.
Unlike symmetric encryption, which uses the same key for both encryption and decryption, RSA employs a pair of keys: a public key for encryption and a private key for decryption. The public key can be freely distributed, while the private key must be kept secret. Data encrypted with the public key can only be decrypted with the corresponding private key.
This fundamental asymmetry is a key strength of RSA, allowing for secure communication without the need to securely exchange secret keys. The security of RSA relies on the computational difficulty of factoring large numbers.
RSA Encryption Algorithm
RSA works by transforming plain text into ciphertext using modular arithmetic and prime numbers. The process involves selecting two large prime numbers, p and q, and calculating their product, n. Euler’s totient function is then used to compute φ(n). A public exponent, e, is chosen, which is relatively prime to φ(n). The private exponent, d, is calculated such that (ed) ≡ 1 (mod φ(n)).
RSA’s explanation for the recent breach details feels a bit murky, doesn’t it? It’s hard to get a clear picture of what exactly happened. This lack of transparency is reminiscent of Microsoft’s struggles in the mobile market, where, as the article no kin do microsoft keeps limping into the mobile era points out, they’ve been rather lackluster.
Hopefully, RSA will provide more concrete information soon to clear up the confusion surrounding the breach.
The public key consists of (n, e), and the private key is (n, d). To encrypt a message M, it is converted into an integer representation, and the ciphertext C is calculated as C = M e (mod n). Decryption is performed as M = C d (mod n).
Types of Security Breaches Affecting RSA Systems
Various vulnerabilities can compromise RSA systems. These include:
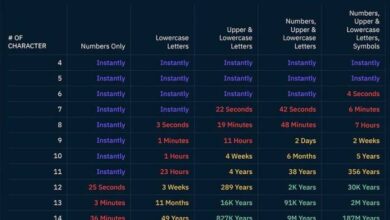
- Brute-force attacks: Attempting to find the private key by trying all possible combinations. This is practically infeasible for large keys, but smaller keys are at risk.
- Factorization attacks: Exploiting weaknesses in the mathematical underpinnings of RSA. Researchers continually search for new mathematical techniques that could make factoring large numbers easier. Advancements in computational power could render certain key sizes vulnerable over time.
- Side-channel attacks: Gathering information about the private key through analyzing the physical resources used to execute RSA calculations. These attacks exploit timing variations, power consumption patterns, or electromagnetic emanations.
- Key management vulnerabilities: Weaknesses in the procedures for generating, storing, and distributing keys. Improper key management can lead to unauthorized access to private keys.
Potential Consequences of a Security Breach
A security breach in an RSA-based system can have severe consequences, including:
- Data breaches: Compromised private keys can expose sensitive data, such as financial information, personal records, or confidential communications.
- Financial losses: Breaches in financial systems can lead to significant financial losses due to fraud or theft.
- Reputational damage: Public disclosure of a security breach can severely damage an organization’s reputation and erode customer trust.
- Legal repercussions: Organizations may face legal action if they fail to adequately protect sensitive data.
General Principles of Information Security
Robust information security practices are essential to mitigate risks associated with RSA and other encryption systems. These include:
- Strong key management: Implementing secure procedures for generating, storing, and distributing keys.
- Regular security audits: Conducting regular assessments to identify and address vulnerabilities.
- Data encryption: Encrypting sensitive data both in transit and at rest.
- Employee training: Educating employees on security best practices to prevent social engineering attacks.
Comparison of Encryption Methods
| Encryption Method | Key Type | Security | Performance | Use Cases |
|---|---|---|---|---|
| RSA | Asymmetric | Relies on large number factorization | Slower than symmetric methods | Key exchange, digital signatures |
| AES | Symmetric | Relies on substitution-permutation network | Faster than RSA | Data encryption at rest and in transit |
| ECC | Asymmetric | Based on elliptic curve cryptography | Generally faster than RSA for comparable security | Mobile devices, IoT |
Understanding the “Foggy” Aspect of the Breach
The RSA security breach, while significant in its impact, was shrouded in a degree of ambiguity regarding the specific details of the attack. This “foggy” aspect, characterized by a lack of readily available information, raises crucial questions about transparency and communication during such incidents. Understanding the reasons behind this ambiguity is vital for improving future security breach responses and building public trust.The vagueness surrounding the RSA breach highlights the complexities of modern security incidents.
Often, the initial reports of a breach contain incomplete or conflicting information, as investigators meticulously piece together the timeline, the attack vectors, and the extent of the damage. This initial uncertainty is a natural part of the investigative process, but it can create a sense of unease and distrust in the affected organizations and the public at large.
Ambiguity and Vagueness in Security Breaches
Ambiguity in security breaches arises from several factors. The attackers often employ sophisticated techniques to mask their actions and evade detection. The attackers might utilize multiple methods to infiltrate systems and exfiltrate data, creating a complex web of activities that may not be immediately apparent. Furthermore, the nature of the attack itself can be convoluted, involving multiple stages, intricate manipulations, or sophisticated malware.
The sheer volume of data involved in complex breaches can also make it difficult to identify the exact scope of the compromise.
Potential Reasons for Lack of Clarity in the RSA Case
Several factors contributed to the lack of immediate clarity regarding the RSA breach. The attackers’ meticulous planning, their use of advanced techniques, and the sophisticated nature of the malware they employed all hindered swift and complete understanding. The attack may have targeted specific data or systems, necessitating a more thorough investigation to fully comprehend the scope of the breach.
The intricate interplay between different systems and the complexity of the attack methods could have contributed to a delay in precise details.
Factors Contributing to Lack of Transparency
A lack of transparency in security breaches can stem from various factors. First, the urgency to contain the breach and prevent further damage can sometimes prioritize operational needs over immediate public disclosure. A rushed response might result in incomplete information being disseminated, or potentially inaccurate details. Second, the investigation process itself can be lengthy and complex, involving multiple stakeholders and different levels of expertise.
Third, the sensitive nature of the data compromised and the potential legal ramifications can influence the level of disclosure. Finally, the need to maintain operational stability and prevent further escalation can sometimes lead to delayed and selective communication.
Communication Strategies for Public Relations
Effective communication during a security breach is critical. A transparent and timely response builds trust and helps mitigate the negative impact. This includes issuing clear, concise, and factual statements about the incident, outlining the steps being taken to contain the breach, and informing the affected parties about their rights and options.
Legal and Ethical Considerations of Incomplete Disclosure
Incomplete disclosure of breach details raises significant legal and ethical concerns. The legal ramifications can vary significantly depending on the jurisdiction and the specific regulations applicable to the situation. In some cases, there may be legal obligations to disclose certain details, such as the nature of the breach and the affected parties. The ethical implications relate to the duty of care owed to stakeholders, including customers, employees, and the public.
Organizations must consider the potential reputational damage, financial losses, and the psychological impact on individuals affected by the breach. Open and honest communication, even when the details are still evolving, can help mitigate these risks.
Potential Impacts of the Breach
The RSA Security breach, a landmark incident in the history of cybersecurity, exposed vulnerabilities in a critical component of digital infrastructure. Understanding the ramifications of such a breach is crucial, not only for the affected parties but also for the broader security landscape. The cascading effects of compromised systems are significant and far-reaching.
Financial Repercussions
The financial fallout from the RSA breach was substantial and multi-faceted. Direct costs included remediation efforts, legal fees, and lost revenue. Furthermore, indirect costs, like decreased investor confidence and reputational damage, contributed significantly to the overall financial burden. The ripple effect across industries that relied on RSA’s security solutions was substantial, leading to increased insurance premiums and the implementation of new security protocols.
Reputational Damage
A security breach, particularly one of the magnitude of the RSA breach, can inflict severe reputational damage. The loss of trust in the company’s ability to protect sensitive data undermines the brand’s credibility and erodes customer loyalty. Customers might seek alternatives and shift their business to competitors, leading to a significant loss of market share. In the aftermath of the breach, RSA had to rebuild trust with its customers, a process that takes time and substantial effort.
Impact on User Trust and Confidence
The RSA breach eroded user trust and confidence in the company’s systems and products. This loss of trust translates into a tangible impact on the company’s bottom line, impacting sales and future business opportunities. Users may be less inclined to adopt RSA’s products or services, choosing alternative solutions perceived as more secure. The long-term implications of such a loss of confidence can be severe, affecting the company’s market position and profitability.
Impact Across Industries
The potential impacts of a data breach vary significantly across different industries. In the financial sector, a breach can lead to significant financial losses, regulatory fines, and reputational damage. In the healthcare industry, the consequences can include patient data breaches, regulatory penalties, and compromised patient safety. The impact on the retail sector may include fraudulent transactions, compromised customer data, and a decline in sales.
Comparing the impact across industries highlights the importance of tailored security measures specific to each sector’s vulnerabilities.
Framework for Assessing Breach Damage
A comprehensive framework for assessing the damage from a security breach should consider several key factors:
- Financial Losses: Direct costs (e.g., remediation, legal fees) and indirect costs (e.g., lost revenue, insurance premiums). Examples include the financial losses incurred by banks and retailers due to fraudulent transactions and the subsequent need for security enhancements.
- Reputational Damage: Loss of customer trust, decline in market share, and damage to brand image. Examples include the decline in consumer confidence following high-profile data breaches and the resulting impact on stock prices.
- Operational Disruptions: Downtime, system outages, and disruptions to business operations. Examples include the temporary closure of retail stores due to system failures following a breach and the subsequent negative impact on revenue and customer service.
- Legal and Regulatory Penalties: Fines, legal settlements, and compliance costs. Examples include significant fines imposed by regulatory bodies for non-compliance and inadequate security measures.
- Loss of Customer Data: Impact on user trust and potential legal implications. Examples include lawsuits and compensation claims brought forth by users whose data was compromised.
By systematically evaluating these factors, organizations can better understand the multifaceted consequences of a security breach and develop effective strategies for mitigation and recovery.
Methods for Addressing the Foggy Details
The RSA breach, like many others, presented a significant challenge in terms of understanding the full scope of the incident. Incomplete or unclear information can exacerbate the damage, creating uncertainty for affected parties and hindering effective recovery. Addressing these “foggy” details requires a proactive and transparent approach, moving beyond initial pronouncements to a comprehensive and detailed response.
The Importance of Clear and Transparent Communication
Effective communication is paramount in a security breach. Transparency builds trust and allows stakeholders to make informed decisions. Delayed or vague responses can amplify the damage and create mistrust, potentially leading to reputational harm. Clear communication should Artikel the nature of the breach, affected systems, impacted data, and steps being taken to mitigate future risks.
Examples of Effective Communication Strategies
Several organizations have demonstrated effective communication strategies during security breaches. For instance, companies often release statements outlining the nature of the breach, steps being taken, and the estimated timeframe for resolution. These statements are typically followed by detailed reports that provide additional context, technical details, and future preventative measures. Another example is consistent updates to affected parties through various channels, such as email, dedicated websites, or social media.
Methods for Identifying and Rectifying Information Gaps
Thorough investigation is crucial for uncovering the full extent of a security breach. This involves a multi-faceted approach, including reviewing security logs, examining system vulnerabilities, and conducting forensic analysis. A comprehensive incident response plan is vital for navigating these investigations effectively. Often, outside cybersecurity experts are engaged to provide objective assessments and help identify any overlooked vulnerabilities or blind spots in the security infrastructure.
Methods for Mitigating the Impact of Incomplete Information
Incomplete information can create significant challenges during a breach response. However, these challenges can be mitigated through proactive risk assessment and planning. This involves developing contingency plans for different scenarios, including partial information. For example, initial responses can focus on containing the damage while additional information is gathered. Building redundancy in the security infrastructure can also minimize the impact of incomplete information by ensuring that other systems can function as backups.
RSA’s explanation for the recent breach is surprisingly vague, leaving many questions unanswered. It’s almost as if they’re trying to keep a lid on the whole thing, which is understandable in a way, given the parallel with Facebook’s recent shift towards more fast-food-style acquisitions. Facebook develops a taste for fast food seems to be a trend that companies are embracing, and perhaps this secrecy is a similar attempt to manage the fallout of such a major shift.
However, this lack of transparency surrounding the RSA breach is certainly raising some eyebrows, and ultimately, it’s not a good look.
Stages of a Security Breach Response
| Stage | Description |
|---|---|
| Preparation | Establishing incident response plans, training personnel, and developing communication protocols. This stage focuses on prevention and preparedness. |
| Detection | Identifying the breach, analyzing the impact, and initiating containment measures. This stage often relies on security monitoring systems. |
| Containment | Stopping the spread of the breach, isolating affected systems, and securing data. This is a crucial stage to prevent further damage. |
| Eradication | Removing the threat, patching vulnerabilities, and restoring affected systems. A comprehensive approach to fixing the problem is critical. |
| Recovery | Restoring systems to normal operations, conducting forensic analysis, and implementing improved security measures. This stage includes rebuilding trust and confidence. |
| Lessons Learned | Evaluating the incident response, identifying weaknesses, and implementing corrective actions to prevent future breaches. This stage focuses on continuous improvement. |
Mitigation Strategies and Prevention
The recent RSA security breach highlights critical vulnerabilities in the digital landscape. Proactive measures and robust security protocols are essential to prevent similar incidents. Addressing the “foggy” details of the breach necessitates a multifaceted approach encompassing improved security measures, enhanced incident response, and a culture of security awareness within organizations.
Proactive Measures to Prevent Future Breaches
A crucial step in preventing future security breaches is implementing comprehensive security protocols. These protocols should cover a broad spectrum, including network security, access control, and data encryption. Strong passwords, multi-factor authentication, and regular security audits are all vital components of a proactive security strategy. Regular vulnerability assessments are also critical in identifying and patching potential weaknesses in systems.
This proactive approach can greatly reduce the risk of successful attacks.
- Network Security: Implementing firewalls, intrusion detection systems (IDS), and intrusion prevention systems (IPS) to monitor and control network traffic are crucial. These systems can identify and block malicious activity before it can compromise systems.
- Access Control: Restricting access to sensitive data and systems based on the principle of least privilege. Implementing role-based access control (RBAC) ensures that users only have the necessary permissions to perform their tasks. This significantly reduces the potential impact of compromised accounts.
- Data Encryption: Encrypting sensitive data both in transit and at rest is vital. Encryption makes data unreadable to unauthorized individuals, even if they gain access to the systems. End-to-end encryption should be considered for all sensitive communications.
- Regular Security Audits: Performing regular security audits to identify vulnerabilities in systems and applications. This helps to identify and fix weaknesses before they are exploited. Vulnerability scanners and penetration testing are effective tools in this process.
Importance of Strong Security Protocols
Robust security protocols are the cornerstone of a secure environment. They define the rules and procedures that organizations must follow to protect their assets. Strong protocols ensure consistent adherence to security best practices, reducing the risk of human error and malicious activity. Effective security protocols are essential to minimize the potential for breaches.
Implementing a Robust Incident Response Plan
A well-defined incident response plan is critical in handling security incidents swiftly and effectively. It Artikels the steps to take in the event of a security breach, including containment, eradication, recovery, and post-incident activities. A comprehensive plan should include clear roles and responsibilities, communication channels, and procedures for escalating incidents.
- Identification: Rapid identification of the incident is crucial. Early detection can significantly reduce the extent of damage.
- Containment: Restricting the impact of the incident by isolating affected systems. This limits the spread of the threat.
- Eradication: Removing the threat from the system. This may involve restoring systems from backups or implementing patches.
- Recovery: Restoring systems and data to their normal operating state.
- Post-Incident Activities: Evaluating the incident, implementing preventative measures, and updating the incident response plan. Lessons learned should be incorporated into future security measures.
Best Practices for Strengthening RSA Systems
Implementing strong authentication methods, regular patching, and secure configuration are crucial for bolstering RSA systems. Using strong and unique passwords, enabling multi-factor authentication, and enforcing regular password changes are vital to enhance the security posture. Regular security awareness training for employees is also recommended. Continuous monitoring and evaluation of the security environment are essential for maintaining a robust security posture.
RSA’s explanation for the recent breach is a bit murky, leaving many questions unanswered. While Google Maps is now incorporating real-time road traffic data, providing a clearer picture of route efficiency, it’s a bit frustrating that the details surrounding the security incident remain so vague. Hopefully, a more comprehensive explanation from RSA will follow soon, allowing us to understand the full scope of the breach.
Security Incident Response Flowchart
A security incident response flowchart Artikels the sequential steps involved in handling a security incident. It visually represents the process from initial detection to post-incident analysis. A well-designed flowchart clarifies the responsibilities of different teams and individuals.
A well-defined incident response plan is critical in handling security incidents swiftly and effectively.
Illustrative Case Studies (Hypothetical): Rsa Explanation Foggy About Breach Details
Understanding the intricacies of security breaches, particularly those involving significant vulnerabilities, requires more than just theoretical knowledge. Analyzing real-world scenarios, even hypothetical ones, helps solidify our comprehension of potential weaknesses and the subsequent fallout. This section delves into illustrative case studies to highlight the challenges and responses involved in such events.
Hypothetical Case Study 1: The “Shadow Data Breach”
A mid-sized financial institution, “Apex Bank,” experienced a security breach categorized as a “shadow data breach.” This involved unauthorized access to a secondary, less-scrutinized database containing customer transaction history, albeit not sensitive personal information. The attackers’ goal wasn’t financial gain, but rather data mining for market research purposes. This highlighted the potential threat from non-financial actors seeking insights from seemingly less sensitive data.
Steps Taken to Address the Breach: Apex Bank immediately launched a forensic investigation to pinpoint the entry point and extent of the breach. They alerted affected customers, implemented enhanced security measures focusing on access controls for secondary databases, and worked with law enforcement. Crucially, they conducted thorough vulnerability assessments to proactively identify and address similar weaknesses in other systems.
Challenges Encountered: The attackers’ use of sophisticated social engineering tactics to gain access to the secondary database proved challenging to detect. The lack of consistent security monitoring across all databases and the slow response time to detect the breach were significant setbacks. The bank faced reputational damage and potential legal ramifications.
Hypothetical Case Study 2: The “Supply Chain Compromise”
A multinational technology company, “InnovateTech,” experienced a security breach triggered by a compromised third-party vendor. A crucial software update, distributed through the vendor, contained malicious code that infiltrated InnovateTech’s internal network, leading to the theft of intellectual property. This scenario underscores the vulnerability of supply chains to malicious actors.
Steps Taken to Address the Breach: InnovateTech immediately suspended all updates from the compromised vendor. They initiated a full internal audit to identify the extent of the damage and launched a forensic analysis to understand the attack vector. The company implemented enhanced due diligence procedures for all third-party vendors, including robust background checks and penetration testing, and also strengthened their incident response plan.
Challenges Encountered: Identifying the precise point of compromise within the supply chain proved complex. The sheer volume of data processed through the compromised vendor’s system presented a significant challenge in isolating the infected data. This scenario also highlighted the need for more robust collaboration between companies and vendors to mitigate supply chain risks.
Hypothetical Case Study 3: The “Insider Threat”
A major healthcare provider, “WellnessCare,” faced a security breach orchestrated by a disgruntled former employee. This disgruntled employee exploited their prior access privileges to steal patient records, leading to a data breach of significant proportions. This highlights the risk of insider threats.
Steps Taken to Address the Breach: WellnessCare immediately terminated the former employee’s access privileges and reported the breach to law enforcement. They conducted a thorough internal investigation, updated their access control policies, and implemented stricter background checks for new hires. Patient notification procedures were immediately initiated. They also strengthened their security awareness training program.
Challenges Encountered: Detecting the insider threat in the initial stages was difficult due to the lack of comprehensive monitoring tools and procedures. The former employee’s access to sensitive data, combined with their insider knowledge, made the breach particularly damaging. Legal and reputational implications were severe.
Table of Hypothetical Case Studies, Rsa explanation foggy about breach details
| Case Study | Brief Description | Identified Causes of the Breach |
|---|---|---|
| Shadow Data Breach | Unauthorized access to a secondary, less-scrutinized database. | Sophisticated social engineering, lack of consistent security monitoring, slow response time. |
| Supply Chain Compromise | Compromised third-party vendor leading to malicious code injection. | Vulnerability in third-party software, lack of robust due diligence procedures. |
| Insider Threat | Disgruntled former employee exploiting prior access privileges. | Lack of comprehensive monitoring tools, inadequate access control policies, inadequate background checks. |
Outcome Summary
In conclusion, the RSA breach highlights the urgent need for transparent and timely communication in handling security incidents. Effective incident response strategies, proactive measures to prevent similar breaches, and robust incident response plans are crucial to maintaining public trust. The hypothetical case studies illustrate the challenges and the importance of proactive security measures. The future of cybersecurity depends on organizations’ ability to learn from these incidents and improve their preparedness for future threats.