Protecting Data Cold Out There
Its cold out there protecting data outside the enterprise firewall. Keeping sensitive information safe when it’s not behind the corporate walls requires a multifaceted approach. This involves understanding the various environments where data resides, from remote worker devices to cloud services and IoT gadgets. We’ll explore the threats, strategies, technologies, and implementation steps necessary to secure this increasingly dispersed data.
This article dives deep into the challenges and solutions surrounding external data protection. From identifying threats to implementing robust security measures, we’ll cover the crucial steps organizations need to take to safeguard their valuable information. We’ll also present illustrative scenarios and case studies to provide practical insights into the realities of external data security.
Defining the Scope of External Data Protection
Protecting data beyond the confines of the enterprise firewall is crucial in today’s interconnected world. This involves a much broader scope than simply the internal network. Data travels freely across various platforms, making it vulnerable to breaches and misuse if not properly secured. Understanding where this data resides and the associated risks is paramount to developing robust protection strategies.
Understanding Data Outside the Enterprise Firewall
Data outside the enterprise firewall encompasses any information that leaves the controlled network perimeter. This includes data transmitted to and from cloud services, remote worker devices, and Internet of Things (IoT) devices. It’s no longer a simple case of data being either inside or outside; data flows constantly between various environments, requiring comprehensive protection strategies.
Types of Exposed Data
Various types of data are exposed when operating outside the enterprise firewall. These include sensitive customer information, financial details, intellectual property, and operational data. Protecting this broad spectrum of data requires a multi-layered approach that considers the specific sensitivity of each type. For instance, customer Personally Identifiable Information (PII) requires more stringent security measures than general operational data.
It’s a chilly environment out there safeguarding data beyond the enterprise firewall. Protecting sensitive information in this climate is a real challenge, especially when considering the current state of the US’s scientific standing – a reputation for innovation that, some argue, is flagging. This decline potentially impacts our ability to develop cutting-edge security solutions, making the job of protecting data even tougher.
Ultimately, the cold hard truth remains – safeguarding data outside the firewall is a constant battle.
Environments Where External Data Resides
Data exists in diverse environments beyond the firewall. These include:
- Remote Worker Devices: Employees working remotely access corporate resources through various devices (laptops, tablets, smartphones). This exposes data to potential vulnerabilities if these devices aren’t adequately secured.
- Cloud Services: Companies increasingly rely on cloud platforms for storage, processing, and collaboration. Data stored in cloud services is vulnerable if the cloud provider’s security measures are inadequate or if user authentication is compromised.
- IoT Devices: Connected devices, like sensors and smart appliances, generate and transmit data. These devices often have limited security features, making them susceptible to exploitation.
Security Risks Associated with Different Environments
The security risks associated with each environment vary significantly. This table highlights the potential threats and vulnerabilities in each case:
| Environment | Security Risks |
|---|---|
| Remote Worker Devices | Malware infections, phishing attacks, unauthorized access, data loss due to device theft or loss, weak passwords, inadequate security software. |
| Cloud Services | Data breaches due to cloud provider vulnerabilities, misconfigurations, unauthorized access by malicious actors, insufficient access controls, inadequate encryption. |
| IoT Devices | Malware infections, denial-of-service attacks, unauthorized access to sensitive data, lack of robust authentication, weak default passwords. |
Assessing the Threats to External Data
Protecting data outside the enterprise firewall requires a deep understanding of the threats it faces. External data is vulnerable to a range of attacks, each with unique characteristics and potential consequences. This vulnerability stems from the very nature of external access, which often necessitates reliance on diverse and potentially less secure systems and networks. A proactive approach to threat assessment is crucial for developing effective mitigation strategies.
Primary Threats Targeting External Data
External data is exposed to a variety of threats. These threats can be broadly categorized into cyberattacks, data breaches, and insider threats. Each category presents distinct challenges and requires tailored security measures.
Cyberattacks
Cyberattacks represent a significant threat to external data, exploiting vulnerabilities in systems and networks to gain unauthorized access or disrupt operations. These attacks often leverage sophisticated techniques, making them difficult to detect and mitigate. Common attack vectors include phishing, malware, and denial-of-service (DoS) attacks.
Data Breaches
Data breaches, encompassing unauthorized access and disclosure of sensitive data, are another major concern. These breaches can stem from various sources, including vulnerabilities in applications, weak passwords, or sophisticated hacking techniques. Attackers may target specific data types, such as customer records or financial information, for resale or malicious use.
Insider Threats
Insider threats are a less visible but equally significant concern. These threats involve individuals within the organization who intentionally or unintentionally compromise data security. This can manifest in malicious actions like data theft or accidental disclosure through negligence or poor security practices. Malicious insiders might act due to financial gain, revenge, or ideological motives.
Attack Vectors and Their Impact
The attack vectors associated with these threats vary considerably, each requiring a different approach to mitigation. Understanding these differences is crucial for implementing effective security measures. The impact of these threats can be significant, encompassing financial losses, reputational damage, and potential legal repercussions.
Table Illustrating Different Attack Methods
| Attack Method | Description | Example | Impact |
|---|---|---|---|
| Phishing | Tricking individuals into revealing sensitive information through deceptive emails or websites. | A fake email claiming to be from a bank asking for account details. | Financial loss, compromised accounts. |
| Malware (e.g., ransomware) | Malicious software designed to damage or disable systems, often encrypting data for ransom. | Ransomware attack encrypting customer databases. | Financial loss, data loss, operational disruption. |
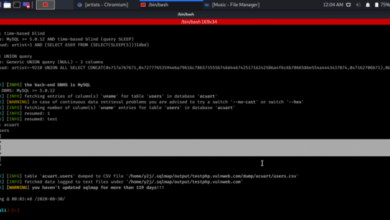
| SQL Injection | Exploiting vulnerabilities in database applications to gain unauthorized access to data. | A malicious SQL query inserted into a web form to retrieve sensitive information. | Data breaches, unauthorized access. |
| Denial-of-Service (DoS) | Overloading a system with traffic to prevent legitimate users from accessing it. | A coordinated attack flooding a company website with traffic, making it unavailable. | Operational disruption, loss of revenue. |
Strategies for Protecting External Data
Protecting sensitive data outside the enterprise firewall requires a multifaceted approach. This involves implementing robust security measures at various points, from data transmission to user access. Effective external data protection necessitates a proactive strategy, addressing potential vulnerabilities and anticipating evolving threats. Careful consideration of employee training and secure remote access solutions are critical components of this comprehensive approach.
Security Measures for External Data
External data protection demands a layered approach. This involves a combination of technical controls, access restrictions, and security awareness training. Implementing encryption, access controls, and multi-factor authentication are crucial elements in this strategy. These measures significantly reduce the risk of unauthorized access and data breaches.
Encryption Methods for External Data
Different encryption methods offer varying levels of security and complexity. Choosing the right method depends on the sensitivity of the data and the specific needs of the organization.
- Symmetric-key encryption, like AES (Advanced Encryption Standard), uses the same key for encryption and decryption. This method is faster and more efficient for large datasets, but key management is critical to avoid compromise.
- Asymmetric-key encryption, such as RSA (Rivest–Shamir–Adleman), uses a pair of keys—a public key for encryption and a private key for decryption. This method is well-suited for secure communication and digital signatures, but it’s computationally more intensive than symmetric-key encryption.
- Hashing algorithms, such as SHA-256, generate unique fingerprints of data. They’re primarily used for data integrity checks, verifying that data hasn’t been tampered with, rather than for full encryption.
Security Awareness Training
A critical aspect of external data protection is ensuring that employees understand the risks and best practices for handling sensitive data. Comprehensive training programs should be mandatory for all personnel who interact with external data.
- Training should cover the organization’s data protection policies, highlighting the importance of confidentiality, integrity, and availability of data.
- Specific scenarios, such as phishing attacks and social engineering tactics, should be addressed to help employees recognize and avoid these threats.
- Regular refresher courses and simulations can reinforce learning and ensure employees remain vigilant against evolving threats.
Secure Remote Access Solutions
Secure remote access solutions are essential for enabling authorized personnel to access enterprise data and applications from outside the firewall. These solutions need to incorporate strong security measures to prevent unauthorized access and data breaches.
- Virtual Private Networks (VPNs) create encrypted connections between remote users and the corporate network. They provide a secure tunnel for data transmission, safeguarding sensitive information during transit.
- Zero Trust Network Access (ZTNA) solutions restrict network access based on the identity of the user and the specific resources they need. This granular approach significantly enhances security by minimizing the attack surface.
- Multi-factor authentication (MFA) adds an extra layer of security to remote access by requiring users to provide multiple forms of verification, such as passwords, security tokens, or biometric data.
Technologies and Tools for Data Protection: Its Cold Out There Protecting Data Outside The Enterprise Firewall
Protecting data outside the enterprise firewall demands a multifaceted approach. Beyond traditional security measures, specialized technologies are crucial for safeguarding sensitive information in remote locations. These technologies must be adaptable to diverse environments and evolving threats. This section delves into the key technologies and tools used for robust external data protection.Cloud environments, remote workforces, and the increasing reliance on third-party services create numerous access points for potential breaches.
It’s definitely a chilly environment out there safeguarding data beyond the enterprise firewall. Protecting sensitive information requires robust security measures, and the constant evolution of threats makes it a real challenge. Thinking about how technology is adapting in other areas, like whether Amazon’s new Kindles tablets are in training are amazons new kindles tablets in training , is a fascinating glimpse into how different sectors are evolving.
Ultimately, though, the core issue of safeguarding data remains critical, and the battle to keep it secure outside those firewalls continues.
Effective data protection strategies require comprehensive tools that address these vulnerabilities, ensuring the confidentiality, integrity, and availability of sensitive data.
Virtual Private Networks (VPNs)
VPNs establish secure connections between users and the corporate network, effectively extending the firewall’s protection to remote locations. They encrypt data transmitted over public networks, such as the internet, preventing unauthorized access. VPNs are a foundational element for securing remote access to sensitive data.
Cloud Security Tools
Cloud environments introduce new security challenges. Cloud security tools are specialized solutions designed to protect data stored and processed in the cloud. These tools can include access control mechanisms, data loss prevention (DLP) systems, and security information and event management (SIEM) tools tailored for cloud environments. They often integrate with existing security infrastructures.
Endpoint Detection and Response (EDR) Systems
EDR systems monitor endpoints, such as laptops and mobile devices, for malicious activity. They provide real-time threat detection and response capabilities, enabling swift containment of potential breaches originating from endpoints outside the corporate network. EDR solutions can be crucial in mitigating threats stemming from compromised or vulnerable devices.
Secure Access Service Edge (SASE)
SASE is a cloud-native security architecture that consolidates multiple security services into a single platform. This platform delivers secure access to applications and data regardless of user location or device. SASE combines various security functions, such as VPNs, firewalls, and cloud access security brokers (CASBs), within a unified architecture. This allows for a more streamlined and efficient approach to securing access to external resources.
Zero-Trust Security Models
Zero-trust security models adopt a strict “never trust, always verify” approach. This model assumes no implicit trust, regardless of the user’s location or device. Zero-trust security enforces granular access controls, verifying every user and device attempting to access resources, even within the organization’s network. This stringent approach minimizes the impact of a potential breach by limiting access to only what is absolutely necessary.
Implementing and Maintaining Data Security
Building a robust external data security program isn’t a one-time project; it’s an ongoing commitment. Establishing and maintaining a secure environment requires a multifaceted approach, addressing both proactive measures and reactive responses to potential threats. This necessitates a comprehensive strategy encompassing policies, procedures, technology, and personnel training. A strong security program must adapt to the ever-evolving threat landscape, ensuring continuous improvement and vigilance.Effective external data protection relies on a proactive and reactive approach, meaning that organizations must not only anticipate and prevent potential threats but also have procedures in place to respond effectively to security incidents.
This proactive-reactive cycle is crucial for maintaining the confidentiality, integrity, and availability of external data.
Establishing a Security Program
A well-structured external data security program starts with a clear definition of responsibilities and policies. This includes outlining acceptable use policies for data, outlining procedures for data handling, and defining the escalation process for security incidents. Establishing clear lines of communication and accountability is paramount to maintaining a strong security posture. Furthermore, the program should incorporate regular reviews and updates based on emerging threats and best practices.
Regular Security Audits and Assessments
Regular security audits and assessments are essential for identifying vulnerabilities and gaps in security controls. These assessments can be conducted internally or by external security experts, and they should cover all aspects of the external data security program, including policies, procedures, technology, and personnel. The results of these assessments should be used to prioritize improvements and enhance the overall security posture.
By regularly evaluating the effectiveness of security measures, organizations can proactively address vulnerabilities and prevent potential breaches.
Handling Security Incidents and Breaches
A well-defined incident response plan is crucial for handling security incidents and breaches. This plan should Artikel the steps to be taken in the event of a breach, including containment, eradication, recovery, and post-incident analysis. Effective communication with stakeholders and affected parties is critical during an incident. The incident response plan should also be regularly reviewed and updated to ensure its effectiveness in responding to emerging threats.
Proactive incident response training for personnel is vital for rapid and effective action in case of an actual incident.
Best Practices for External Data Security
| Category | Best Practice | Explanation |
|---|---|---|
| Policy & Procedures | Establish clear data handling policies and procedures for external data | Explicitly define who can access what data, when, and under what circumstances. This should include policies for data encryption, access control, and data deletion. |
| Technology | Implement strong encryption for data in transit and at rest | Employ industry-standard encryption protocols to protect sensitive data both when it’s being transmitted and stored. |
| Personnel | Regular security awareness training for employees | Train employees on recognizing and avoiding phishing attacks, social engineering tactics, and other common security threats. |
| Monitoring | Implement robust monitoring and logging | Monitor systems and activities for suspicious behavior and anomalies. Logging provides a historical record for investigation and analysis. |
| Incident Response | Develop and test a comprehensive incident response plan | Artikel the steps to be taken in the event of a security incident. Regularly test the plan to ensure it’s effective. |
Illustrative Scenarios

Protecting data outside the enterprise firewall presents unique challenges. Understanding potential vulnerabilities and how to respond is crucial. This section explores a detailed scenario of external data compromise to highlight the issues involved and preventive measures.
Protecting data outside the enterprise firewall is a tricky business, especially in this cold weather. The recent European uproar over street view privacy, as detailed in this piece on european racket over street view privacy spawns probes , highlights just how complex and nuanced safeguarding data can be. It underscores the importance of vigilance and proactive measures, emphasizing that protecting data outside the corporate walls is a constant challenge.
External Data Breach at a Remote Sales Team
A small, rapidly growing software company utilizes a cloud-based CRM system for its remote sales team. This system allows external access to sales data for lead management and customer interaction. The team relies on individual employee accounts with weak passwords, many of which are reused across personal and work accounts. This creates a vulnerability for attackers to compromise multiple accounts through phishing or brute-force attacks.
Compromise Scenario
A sophisticated phishing campaign targeting the sales team successfully tricks several employees into clicking on malicious links disguised as legitimate company updates. These links install malware on the employees’ personal devices. The malware silently gathers credentials and other sensitive information from the infected devices, including the cloud-based CRM login credentials. Once the attackers gain access, they download and exfiltrate critical sales data, customer contact information, and proprietary product information.
Causes of the Incident
Several factors contributed to this incident:
- Weak employee passwords and reuse of passwords across accounts.
- Lack of robust multi-factor authentication (MFA) for the cloud CRM.
- Failure to implement strong endpoint security solutions on employee devices.
- Inadequate cybersecurity awareness training for the remote sales team.
- A sophisticated phishing campaign targeting the company.
Consequences of the Incident
The consequences of the data breach include:
- Reputational damage and loss of customer trust.
- Financial losses due to potential legal actions, regulatory fines, and the cost of data recovery.
- Loss of competitive advantage due to the disclosure of sensitive product information.
- Potential compromise of customer data and subsequent identity theft.
- Significant disruption to business operations and sales processes.
Preventive Measures
To prevent a similar incident, the company should have implemented the following measures:
- Strong Password Policies: Enforce strong, unique passwords for all employee accounts, combined with multi-factor authentication (MFA).
- Robust Endpoint Security: Implement endpoint detection and response (EDR) solutions to detect and block malware on employee devices.
- Regular Security Awareness Training: Conduct regular cybersecurity awareness training to educate employees on phishing attacks and other threats.
- Data Loss Prevention (DLP) Measures: Implement DLP tools to monitor and prevent sensitive data from leaving the organization’s control.
- Regular Security Audits: Conduct regular security audits to identify and address vulnerabilities in the system and processes.
Mitigation Strategies, Its cold out there protecting data outside the enterprise firewall
In the event of a breach, the following mitigation strategies should be employed:
- Immediate Containment: Immediately isolate infected systems and disable access to compromised accounts.
- Data Recovery: Implement a robust data recovery plan to restore lost or compromised data.
- Incident Response Plan: Activate the company’s incident response plan to manage the crisis effectively.
- Notification and Communication: Notify affected customers and stakeholders promptly and transparently.
- Forensic Investigation: Conduct a thorough forensic investigation to determine the extent of the breach and identify the root cause.
Case Studies of Data Breaches (Illustrative)
Protecting data outside the enterprise firewall is a crucial aspect of modern security. Understanding how breaches occur and their impact is essential for developing robust preventative measures. This section presents illustrative case studies to highlight common vulnerabilities and potential consequences.Illustrative breaches, while not referencing specific companies, provide valuable lessons. The characteristics of these breaches, the methods employed, and the impact on the organizations demonstrate the importance of proactive security strategies.
Analyzing these incidents helps to identify patterns and develop preventative measures that can minimize the risk of similar events.
Characteristics of a Hypothetical Data Breach
This hypothetical breach involves a medium-sized e-commerce company that primarily operates through a cloud-based platform. The company relies heavily on third-party services for payment processing and customer support. The breach occurred due to a vulnerability in the third-party payment gateway, which allowed unauthorized access to customer credit card information.
Methods Used in the Breach
The attackers exploited a known vulnerability in the third-party payment gateway’s software. This vulnerability allowed them to inject malicious code that intercepted customer data during transactions. The attackers then used sophisticated tools to exfiltrate the stolen data.
Impact of the Breach on the Organization
The breach resulted in significant financial losses due to chargebacks and fraud. The company’s reputation suffered, leading to a loss of customer trust and reduced sales. Legal ramifications, including regulatory fines and lawsuits, were also a considerable consequence. The breach caused significant disruption to the company’s operations as they worked to rectify the situation.
Preventative Measures to Mitigate Risks
Several preventative measures could have mitigated the risk of this breach:
- Thorough Vendor Due Diligence: The company should have conducted a more rigorous assessment of the third-party vendor’s security practices before integrating their services. This includes reviewing the vendor’s security certifications, compliance records, and incident response plan. Regular security audits of third-party vendors are essential for maintaining a strong security posture.
- Vulnerability Management Program: Implementing a comprehensive vulnerability management program would have allowed the company to identify and address the vulnerability in the third-party payment gateway before it was exploited. This includes regularly scanning systems for known vulnerabilities and promptly patching any discovered issues.
- Multi-Factor Authentication (MFA): Implementing MFA for all critical systems and accounts would have significantly increased the security posture. This would have made it more difficult for attackers to gain access to sensitive data even if they had compromised credentials.
- Data Encryption: Encrypting sensitive data both in transit and at rest would have significantly reduced the impact of a breach. This would have made the stolen data useless to the attackers.
Additional Considerations for Data Protection
The above-mentioned preventative measures highlight the importance of a proactive approach to data security. Organizations should not only focus on reacting to breaches but also on implementing measures to prevent them. A layered approach to security, incorporating multiple controls and technologies, is crucial to mitigate risks effectively. Regular security awareness training for employees is also essential, as human error often plays a significant role in data breaches.
Conclusion
Protecting data outside the enterprise firewall is a continuous process, demanding constant vigilance and adaptation to evolving threats. Implementing the strategies discussed, from robust encryption to zero-trust models, is crucial for safeguarding sensitive information. This comprehensive guide provides a framework for building a secure external data environment, equipping organizations with the knowledge and tools to navigate the complexities of today’s threat landscape.