Malware on the Move McAfee Report
Malware is on the move reports McAfee, signaling a significant shift in cyber threats. This report unveils emerging trends in malware evolution, highlighting evolving tactics and techniques employed by malicious actors. Different types of malware are becoming more prevalent, each with unique characteristics and motivations. Understanding these changes is crucial for both businesses and individual users to effectively mitigate risks and protect themselves.
The report examines the impact of these evolving threats on businesses, ranging from financial losses to operational disruptions. Individual users are also at risk, facing potential data breaches and identity theft. Strategies to mitigate these risks, along with potential costs for businesses of varying sizes, are also analyzed. Furthermore, the report delves into effective detection and prevention strategies, outlining the importance of robust security measures and best practices for both businesses and individuals.
Emerging Malware Trends
Malware continues to evolve, adapting to security measures and exploiting new vulnerabilities. This dynamic nature necessitates a constant vigilance in identifying and mitigating emerging threats. The shift in tactics and techniques employed by attackers is a critical aspect of this evolution, moving from simple infections to sophisticated campaigns. This report delves into the key trends in malware evolution, focusing on the tactics and techniques, the prevalent types of malware, and the motivations behind their creation.
McAfee’s report on the ever-evolving malware landscape is a stark reminder that digital threats are constantly adapting. This shift mirrors the broader trend where the best and brightest minds are increasingly gravitating towards the digital sector, as seen in articles like prints best and brightest go to the digital side. This means the need for robust cybersecurity measures is more critical than ever, especially given the dynamic nature of the malware threats.
Shifting Tactics and Techniques, Malware is on the move reports mcafee
Malware actors are increasingly employing sophisticated techniques to evade detection and achieve their objectives. A key trend is the use of polymorphic and metamorphic malware, which constantly alters its code structure to avoid signature-based detection. Advanced persistent threats (APTs) are also becoming more common, characterized by stealthy and sustained attacks targeting specific organizations or individuals. This shift towards targeted and sophisticated attacks reflects a move away from indiscriminate spamming and towards more personalized and impactful campaigns.
Attackers are also leveraging legitimate tools and infrastructure, making detection even more challenging.
Prevalent Malware Types
Several types of malware are emerging as significant threats. Ransomware continues to be a dominant force, with attackers leveraging encryption to extort payments. The sophistication of ransomware attacks is increasing, including double extortion tactics where attackers threaten to leak stolen data if a ransom isn’t paid. Another notable trend is the rise of fileless malware, which resides entirely in memory and avoids traditional file-based detection methods.
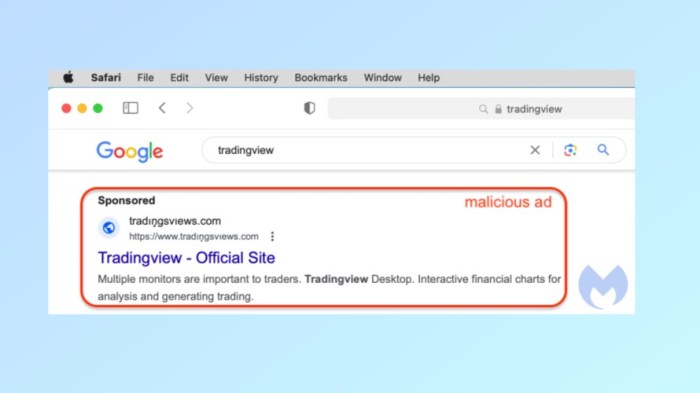
This type of malware often utilizes legitimate system processes to carry out malicious actions. Finally, the continued use of phishing campaigns and social engineering tactics remains prevalent, as these methods exploit human vulnerabilities to gain access to sensitive information.
Motivations Behind Malware Creation
The motivations behind malware creation are diverse and often intertwined. Financial gain is a primary driver, with ransomware attacks and data breaches frequently aimed at extracting money. Espionage and sabotage are also significant motivations, with state-sponsored actors often targeting sensitive information or critical infrastructure. Ideological motivations can also play a role, with malware used to disrupt or damage systems associated with political opponents or specific causes.
Security reports are buzzing about malware on the move, and McAfee is sounding the alarm. While the world of tech is constantly evolving, it’s important to remember that this rapid advancement in graphics technology, like NVIDIA Optimus giving laptops a graphical gearshift, NVIDIA Optimus gives laptops a graphical gearshift , doesn’t mean that cyber threats are going away.
We still need to stay vigilant and proactive in protecting our systems from the ever-evolving malware landscape.
The availability of readily accessible malware kits and tools further fuels the creation and distribution of malicious software.
Comparison of Common Malware Types
| Malware Type | Infection Method | Common Characteristics | Impact |
|---|---|---|---|
| Ransomware | Exploiting vulnerabilities in software, phishing emails, malicious downloads. | Encrypts files, demands payment for decryption. Often includes data exfiltration threats. | Financial losses, data loss, business disruption. |
| Fileless Malware | Leveraging legitimate system processes, memory exploitation, and scripting languages. | Avoids traditional file-based detection, making it difficult to identify and remove. | System compromise, data breaches, potential for long-term damage. |
| Phishing | Social engineering techniques, deceptive emails, fake websites. | Targets user credentitals, exploits trust and psychological manipulation. | Data breaches, financial losses, reputational damage. |
| Advanced Persistent Threats (APTs) | Targeted attacks against specific organizations or individuals, utilizing multiple tactics and techniques to gain sustained access. | Highly sophisticated, stealthy, and persistent. | Significant data breaches, operational disruption, potential for long-term espionage. |
Impact on Businesses and Users
Malware attacks are a pervasive threat in today’s digital landscape, impacting businesses and individuals alike. The consequences can range from significant financial losses to severe operational disruptions, highlighting the critical need for robust security measures. This discussion delves into the specific impact on businesses and users, examining the potential consequences and mitigation strategies.Malware attacks can have devastating effects on businesses, leading to a cascade of negative outcomes.
Financial losses are often substantial, encompassing direct costs associated with incident response, data recovery, and legal fees, as well as indirect costs like lost productivity and reputational damage.
McAfee’s recent report on the surging malware activity is a stark reminder of the ever-evolving threat landscape. This, combined with Microsoft’s push to attract developers with their new WinPho7 toolset, microsoft vies for dev attention with winpho7 toolset , highlights the crucial need for robust security measures. The constant evolution of malware means staying ahead of the curve is more important than ever, regardless of the developer tools being released.
Consequences for Businesses
Businesses of all sizes face considerable risks from malware attacks. These attacks can disrupt operations, leading to lost revenue, diminished productivity, and damage to the company’s reputation. The specific impact varies depending on the type of malware and the preparedness of the business.
- Financial Losses: Malware attacks can result in substantial financial losses. These can include costs associated with incident response, data recovery, and legal fees, but also indirect costs such as lost productivity and reputational damage.
- Operational Disruptions: Malicious software can cripple business operations. Critical systems can be compromised, leading to service outages, delays in production, and decreased efficiency.
- Data Breaches: Malware often targets sensitive business data, including customer information, intellectual property, and financial records. Such breaches can result in regulatory fines, legal action, and significant reputational damage.
- Reputational Damage: A successful malware attack can severely damage a company’s reputation. Customers may lose trust in the organization, leading to a decline in sales and market share.
Consequences for Users
Individual users are also vulnerable to malware attacks. The potential risks extend beyond mere inconvenience, encompassing personal data breaches and identity theft.
- Data Breaches: Malware can compromise personal data, including financial information, passwords, and sensitive documents. This can lead to identity theft and financial losses.
- Identity Theft: Stolen personal data can be used to open fraudulent accounts, make unauthorized purchases, or obtain loans in the victim’s name.
- Financial Losses: Malware can directly steal money from bank accounts or online wallets. Victims may also incur charges for unauthorized transactions.
- Emotional Distress: Experiencing a malware attack can be emotionally distressing. Victims may experience anxiety, frustration, and a loss of trust in online systems.
Mitigation Strategies for Businesses
Proactive measures are crucial in mitigating the risks associated with malware attacks. Implementing robust security practices is essential to safeguard businesses from malicious activities.
- Strong Password Policies: Implementing strong password policies, enforcing regular password changes, and using multi-factor authentication can significantly reduce the risk of unauthorized access.
- Regular Software Updates: Keeping software updated with the latest security patches is crucial in preventing known vulnerabilities from being exploited.
- Firewall Protection: Implementing robust firewalls to monitor and control network traffic can prevent unauthorized access and limit the impact of malicious attacks.
- Employee Training: Educating employees about cybersecurity best practices, such as recognizing phishing emails and avoiding suspicious links, is vital in preventing malware infections.
Potential Costs of Malware Attacks
The financial impact of a malware attack can vary significantly based on the size of the business. Smaller businesses may face significant challenges in recovering from an attack, while larger corporations have more resources to allocate to the process.
| Business Size | Estimated Costs | Impact on Operations | Recovery Time |
|---|---|---|---|
| Small Business (1-10 employees) | $10,000 – $50,000 | Significant disruption to daily operations; potential closure | 2-6 weeks |
| Medium-Sized Business (11-50 employees) | $50,000 – $250,000 | Partial disruption to operations; potential loss of clients | 4-8 weeks |
| Large Enterprise (51+ employees) | $250,000+ | Significant disruption to operations; potential reputational damage | 8+ weeks |
Detection and Prevention Strategies
Malware is a constant threat in today’s digital landscape, impacting businesses and individuals alike. Robust security measures are crucial to mitigating the risks associated with malware infections. Proactive strategies, encompassing both preventative measures and reactive responses, are essential for safeguarding sensitive data and maintaining operational continuity.Effective security measures go beyond simply installing antivirus software. A multi-layered approach, incorporating diverse security tools and vigilant user practices, is vital for a comprehensive defense against malware.
This involves recognizing potential threats, understanding attack vectors, and implementing appropriate countermeasures. A strong security posture demands constant vigilance and adaptation to evolving malware tactics.
Importance of Robust Security Measures
Robust security measures are paramount in preventing malware infections. They create a strong defense against the constant barrage of cyberattacks, reducing the likelihood of data breaches, system disruptions, and financial losses. Security measures protect critical infrastructure, safeguard sensitive information, and maintain business continuity in the face of evolving threats.
Recommended Security Practices for Businesses and Individuals
Implementing sound security practices is critical for both businesses and individuals. These practices include regular software updates, cautious handling of emails and attachments, and strong password management. For businesses, proactive security training for employees is crucial to prevent phishing attacks and other social engineering tactics.
- Regular Software Updates: Keeping software, operating systems, and applications up-to-date is vital. Updates often include critical security patches that address vulnerabilities exploited by malware. Outdated software exposes systems to known exploits, making them susceptible to attacks. Regular updates significantly reduce the risk of infection.
- Strong Passwords: Use strong, unique passwords for all accounts. Avoid easily guessable passwords and utilize password managers to securely store and manage complex passwords. Strong passwords are a first line of defense against unauthorized access.
- Phishing Awareness: Educate yourself and your employees about phishing attacks. Be wary of suspicious emails, links, and attachments. Verify requests for sensitive information through legitimate channels. Phishing awareness training helps individuals and organizations avoid falling prey to social engineering scams.
- Data Backups: Regularly back up important data. This ensures that even if a system is compromised, crucial information can be restored. Data backups provide a safety net in case of ransomware attacks or other malware-related incidents.
Role of Cybersecurity Solutions
Cybersecurity solutions play a critical role in detecting and mitigating malware threats. These solutions, including antivirus software, firewalls, and intrusion detection systems, actively monitor systems for malicious activity. They identify and block threats, helping to prevent infections and minimize damage. These solutions continuously evolve to address new and emerging malware threats.
Cybersecurity Tools and Their Functionalities
| Tool | Functionality | Strengths | Weaknesses |
|---|---|---|---|
| Antivirus Software | Scans files and programs for known malware signatures and suspicious behavior. | Effective at detecting known malware, real-time protection. | May miss new or zero-day threats, performance overhead. |
| Firewall | Controls network traffic, blocking unauthorized connections and preventing malicious traffic from entering the network. | Basic security layer, prevents unauthorized access. | Requires configuration, can block legitimate traffic. |
| Intrusion Detection System (IDS) | Monitors network traffic for malicious activity and notifies administrators of suspicious patterns. | Detects anomalies and potential threats in real-time. | False positives are common, requires expertise for proper configuration. |
| Endpoint Detection and Response (EDR) | Provides comprehensive security for individual devices (endpoints), detecting and responding to threats in real-time. | Advanced threat detection, automated incident response. | Can be expensive, requires integration with other systems. |
The Role of Cybersecurity Professionals
Cybersecurity professionals are the frontline defense against the ever-evolving landscape of malware threats. Their expertise, coupled with continuous learning and adaptation, is crucial in protecting businesses and individuals from the devastating consequences of malicious attacks. The ability to identify, analyze, and respond to emerging threats requires a unique blend of technical skills, strategic thinking, and a deep understanding of human behavior.Cybersecurity experts are not just technicians; they are critical thinkers and problem-solvers who understand the intricate workings of modern digital systems.
They play a pivotal role in safeguarding sensitive data, preventing financial losses, and maintaining the operational integrity of organizations. Their work extends beyond simply detecting and removing malware; it encompasses proactive measures to prevent future attacks and fortify defenses against new threats.
Critical Skills for Cybersecurity Professionals
Cybersecurity professionals require a diverse skillset to effectively combat emerging malware threats. Technical expertise in various programming languages, operating systems, and network protocols is essential. This expertise allows them to analyze malware behavior, understand attack vectors, and develop effective countermeasures.
Continuous Learning and Adaptation in Cybersecurity
The cybersecurity field is constantly evolving, requiring professionals to adapt to new threats and technologies. Staying current with the latest advancements in malware analysis, threat intelligence, and security tools is paramount. This involves continuous learning through training programs, industry conferences, and self-directed study. Keeping up-to-date on emerging attack patterns, exploiting vulnerabilities, and the latest defensive strategies are vital for maintaining effectiveness.
Continuous monitoring of the threat landscape through specialized tools and platforms is a key aspect of this continuous learning process.
Strategies and Methodologies Used by Cybersecurity Professionals
Cybersecurity professionals employ a variety of strategies and methodologies to combat malware threats. These strategies include:
- Threat Intelligence Gathering and Analysis: Cybersecurity professionals leverage threat intelligence feeds, security research reports, and other resources to stay informed about emerging threats. This analysis involves identifying patterns, understanding attacker motivations, and developing targeted defenses. For example, analyzing malware samples to identify their capabilities, potential targets, and distribution channels is a crucial step.
- Vulnerability Assessment and Penetration Testing (VAPT): Identifying vulnerabilities in systems and networks is a proactive approach to security. Penetration testing simulates real-world attacks to assess the effectiveness of security controls. This helps organizations proactively identify and address potential weaknesses before malicious actors exploit them. A thorough vulnerability assessment helps to prioritize remediation efforts.
- Incident Response Planning and Execution: Developing and executing incident response plans is crucial for mitigating the impact of security breaches. This includes defining roles and responsibilities, establishing communication channels, and implementing procedures for containment, eradication, and recovery. For example, a detailed incident response plan for a ransomware attack would Artikel steps to contain the infection, recover data, and prevent future occurrences.
Essential Tools and Technologies Used
Cybersecurity professionals utilize various tools and technologies to analyze, detect, and respond to malware threats. These include:
- Antivirus and Anti-malware Software: These tools are essential for detecting and removing known malware threats. However, their effectiveness is limited against sophisticated, zero-day attacks, requiring advanced techniques.
- Intrusion Detection and Prevention Systems (IDS/IPS): These systems monitor network traffic for malicious activity and block or alert on suspicious patterns. IDS/IPS systems are vital in preventing unauthorized access and mitigating potential damage.
- Security Information and Event Management (SIEM) Systems: These tools collect and analyze security logs from various sources to identify patterns and anomalies that could indicate a security breach. This proactive approach allows for rapid detection and response to threats.
Case Studies and Examples
Malware attacks are a constant threat to businesses and individuals alike. Understanding the tactics and techniques employed by attackers is crucial for developing effective defense strategies. Analyzing past attacks, their impacts, and the lessons learned provides invaluable insights into the evolving landscape of cyber threats. This section will present specific case studies to illustrate the practical implications of various malware types and the importance of proactive security measures.
Recent Malware Attacks and Their Impacts
Analyzing recent malware attacks reveals a pattern of sophisticated techniques employed by attackers. These attacks often target vulnerabilities in software or systems, exploiting human error or organizational weaknesses to gain unauthorized access. The consequences can range from financial losses to reputational damage and significant disruption of operations.
| Case Study | Malware Type | Impact | Lessons Learned |
|---|---|---|---|
| Ryuk Ransomware Attacks (2018-Present) | Ransomware | Significant financial losses for organizations in various sectors, including healthcare and manufacturing. Data encryption and system downtime caused substantial operational disruption and recovery costs. | Organizations need robust data backup and recovery plans. Regular security awareness training for employees is crucial to prevent social engineering tactics used in many ransomware campaigns. Patching vulnerabilities promptly is essential. |
| NotPetya Malware Outbreak (2017) | Widespread, destructive malware | Global supply chain disruption and significant financial losses. The malware infected numerous organizations worldwide, causing widespread operational issues and impacting global trade. | Supply chain security is paramount. Comprehensive security assessments of third-party vendors and suppliers are essential. Having redundant systems and backup data is critical for maintaining operations during a significant disruption. |
| Emotet Malware Campaign (2014-Present) | Malware used as a delivery mechanism for other threats | Used as a stepping stone for other malware (such as ransomware), resulting in widespread data breaches and financial losses. The ability of Emotet to compromise systems and evade detection makes it a significant threat. | Multi-layered security is essential to prevent malware from establishing a foothold. Monitoring network traffic for unusual activity and suspicious connections is critical. |
Attacker Tactics and Techniques
Attackers often leverage a combination of sophisticated tactics and techniques to successfully infiltrate systems. These include social engineering, exploiting known vulnerabilities, and using advanced persistent threats (APTs). Understanding these techniques is crucial for effective defense strategies. Malware authors frequently adapt their tactics in response to evolving security measures.
Importance of Understanding Malware Characteristics
Understanding the characteristics of different malware types is vital for effective defense. Identifying the type of malware, its propagation methods, and the tactics used in the attack allows security teams to implement appropriate countermeasures and mitigate potential damage. Knowing the behavior of malware assists in identifying and blocking malicious activity.
Future of Malware
The digital landscape is constantly evolving, and with it, the nature of malware. Predicting the future of malware is a complex task, but by analyzing current trends and emerging technologies, we can gain insights into potential future threats and develop proactive strategies for mitigation. Understanding the motivations and tactics of malicious actors is crucial to staying ahead of the curve.
Emerging Malware Development Trends
The evolution of malware is driven by the relentless pursuit of innovation by cybercriminals. This includes sophisticated techniques to bypass traditional security measures, leverage new technologies for distribution, and exploit emerging vulnerabilities in software and hardware. Cybercriminals are increasingly targeting specific industries and individuals with tailored attacks, emphasizing the importance of a layered security approach.
Impact of New Technologies on Malware Evolution
New technologies significantly impact malware evolution. The rise of IoT devices, for example, presents new attack vectors, as these devices often have limited security features. Cloud computing, while offering numerous advantages, also introduces new vulnerabilities and attack surfaces. The use of artificial intelligence (AI) is transforming malware development, enabling the creation of more sophisticated and evasive attacks. The increased reliance on machine learning (ML) for malware detection necessitates constant adaptation by cybercriminals.
Potential Emerging Threats and Vulnerabilities
Several emerging threats and vulnerabilities warrant attention. The increasing sophistication of AI-powered malware is a significant concern. Such malware can adapt to defenses in real-time, making detection and mitigation challenging. Supply chain attacks remain a persistent threat, as malicious actors exploit vulnerabilities in software development processes to infect numerous systems. Furthermore, the proliferation of vulnerabilities in newly emerging technologies like 5G networks poses a critical risk.
Potential Countermeasures to Address Future Threats
Robust countermeasures are crucial to address these future threats. Developing proactive security measures that anticipate and adapt to new attack vectors is essential. Improving threat intelligence gathering and sharing among organizations is crucial for identifying emerging threats. Investing in advanced security technologies, such as AI-powered threat detection systems, can help identify and mitigate evolving attacks. Ultimately, promoting a culture of security awareness and education within organizations is paramount to safeguarding against emerging threats.
A combination of these measures is vital to mitigate the evolving landscape of malware threats.
Outcome Summary: Malware Is On The Move Reports Mcafee

In conclusion, McAfee’s report underscores the ever-evolving nature of malware threats. Understanding the motivations behind these attacks, the impact on businesses and users, and the importance of proactive defense strategies is paramount. The report emphasizes the critical role of cybersecurity professionals and the importance of continuous learning and adaptation in the face of emerging threats. Ultimately, staying informed and prepared is key to combating the ever-present threat of malware.







