Pentagon Yep We Got Hacked
Pentagon: We Got Hacked – Unraveling the Implications of a Cybersecurity Breach
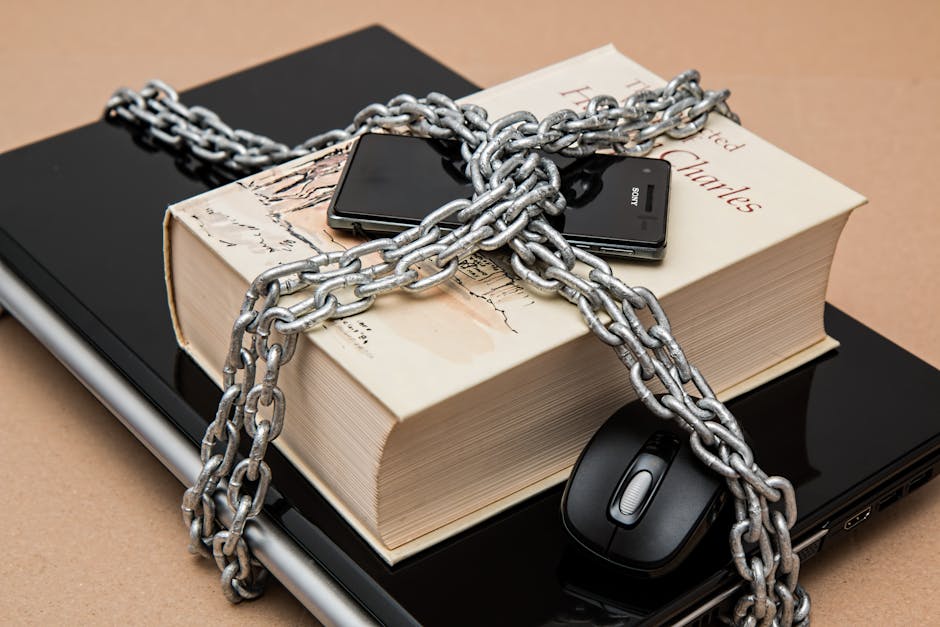
The chilling announcement, "Pentagon: We Got Hacked," sends shockwaves through national security circles and ignites a firestorm of questions regarding the integrity of the United States’ most sensitive defense information. This isn’t a hypothetical scenario; it’s a stark reality that has been faced by the Department of Defense (DoD) on multiple occasions, each instance underscoring the persistent and evolving threat landscape in cyberspace. Understanding the gravity of such a breach requires a deep dive into the types of data potentially compromised, the sophisticated methods employed by adversaries, the far-reaching consequences for national security and global stability, and the continuous, albeit often behind-the-scenes, efforts to fortify defenses. The cybersecurity battleground is no longer confined to physical borders; it is a pervasive, invisible war where critical infrastructure, classified intelligence, and operational plans are constantly under siege.
The Pentagon, as the headquarters of the U.S. Department of Defense, is a repository of unparalleled strategic importance. Its networks are designed to house and process an extraordinary volume of highly classified information, ranging from troop movements and weapon system designs to intelligence assessments, diplomatic strategies, and top-secret operational plans. A successful hack into these systems represents a catastrophic intelligence coup for any adversary. Imagine blueprints for advanced stealth aircraft falling into the wrong hands, enabling adversaries to develop countermeasures and nullify years of technological superiority. Consider troop deployment data being leaked, putting soldiers’ lives at risk by revealing their locations and tactical objectives. Think about the ramifications of classified intelligence on foreign governments and clandestine operations being exposed, potentially destabilizing international relations and jeopardizing long-term U.S. foreign policy objectives. The very fabric of national security is woven with the threads of this information, and a breach at this level can unravel the entire tapestry.
The methodologies employed by state-sponsored actors and sophisticated cybercriminal groups to penetrate the Pentagon are as diverse as they are insidious. Spear-phishing attacks, where tailored emails are sent to specific individuals within the DoD, often impersonating trusted colleagues or superiors, are a common entry point. These emails can trick unsuspecting personnel into clicking malicious links or downloading infected attachments, thereby granting attackers access to the internal network. Exploiting zero-day vulnerabilities, which are previously unknown flaws in software or hardware, presents an even more formidable challenge. These vulnerabilities allow attackers to bypass existing security measures before they can be patched, making them highly prized by nation-state actors. Supply chain attacks, targeting third-party vendors and contractors who have access to DoD systems, offer another avenue for infiltration. Compromising a single vendor can provide a backdoor into the Pentagon’s more secure networks, a tactic that has proven devastatingly effective in numerous high-profile breaches. Moreover, advanced persistent threats (APTs) represent a sustained and covert campaign, where attackers establish a long-term presence within a network, slowly exfiltrating data over extended periods without triggering immediate alarms. These tactics are not crude smash-and-grab operations; they are meticulously planned and executed campaigns by highly skilled individuals or groups with significant resources and intent.
The consequences of a Pentagon hack extend far beyond the immediate loss of sensitive data. On a strategic level, it can erode the United States’ military advantage, forcing a costly and time-consuming reassessment of defense strategies and technological investments. Adversaries gaining access to classified operational plans could preempt U.S. military actions, rendering them ineffective or even turning them against American forces. Economically, the fallout can be immense. The cost of investigating the breach, remediating compromised systems, and rebuilding trust can run into billions of dollars. Furthermore, companies that have partnered with the DoD and whose data has been compromised may face significant financial penalties and reputational damage, leading to a ripple effect across the defense industrial base. Geopolitically, such a breach can destabilize international relations. The exposure of classified intelligence regarding allies or adversaries can create diplomatic crises, undermine trust between nations, and embolden hostile actors. The psychological impact on the American public and military personnel can also be profound, fostering a sense of vulnerability and eroding confidence in the government’s ability to protect its citizens and its secrets.
In response to the ever-present threat, the Pentagon and the wider DoD have been engaged in a continuous, multi-faceted effort to bolster their cybersecurity defenses. This includes investing heavily in advanced threat detection and prevention technologies, such as artificial intelligence-powered intrusion detection systems, behavioral analytics, and robust endpoint security solutions. Regular vulnerability assessments and penetration testing are conducted to identify and rectify weaknesses before they can be exploited. A critical component of this defense strategy is the implementation of stringent access controls and multi-factor authentication to limit unauthorized entry. Furthermore, the DoD is heavily invested in personnel training and awareness programs, recognizing that the human element remains one of the most vulnerable points in any cybersecurity architecture. Educating personnel about phishing tactics, social engineering, and secure data handling practices is paramount. The development and deployment of secure software development practices and the rigorous vetting of third-party vendors are also integral to hardening the defense perimeter. The concept of "zero trust" architecture, where no user or device is inherently trusted, regardless of their location, is increasingly being adopted to compartmentalize networks and limit the lateral movement of attackers.
The ongoing nature of cyber warfare necessitates a proactive and adaptive approach. The DoD actively engages in intelligence gathering and analysis to understand the evolving tactics, techniques, and procedures (TTPs) of adversaries. This intelligence informs the development of new defense strategies and the deployment of counter-measures. Collaboration with international allies and private sector cybersecurity firms is also crucial, fostering a shared understanding of threats and enabling a coordinated response. The formation of specialized cyber command units, such as U.S. Cyber Command, reflects the growing importance of offensive and defensive cyber capabilities. These units are responsible for protecting DoD networks, conducting cyber operations, and providing cyber support to military commanders. The challenge is not merely to defend against current threats but to anticipate and prepare for future ones, a task that requires constant innovation and significant investment in both technology and human capital. The race between attackers and defenders is perpetual, with each side constantly seeking an advantage.
The implications of a successful Pentagon hack are a stark reminder of the critical importance of cybersecurity in the 21st century. The digital realm has become an undeniable theater of operations, and the consequences of a breach at the highest levels of national defense are profound and far-reaching. It necessitates a continuous cycle of assessment, adaptation, and investment. The battle for information dominance is waged daily, and the integrity of the nation’s most sensitive secrets depends on the unwavering commitment to cybersecurity resilience. The phrase "Pentagon: We Got Hacked" serves as a somber and urgent call to action, highlighting the persistent vulnerability and the imperative for a vigilant and technologically advanced defense against the ever-present specter of cyber intrusion. It underscores that in the age of information warfare, national security is inextricably linked to digital security.